The cyber economy is booming. Apogee recognizes this and encourages their clients to be alert to the fact that the world revolves around online access and as a result, there is a great need for firms to create multiple layers of security to protect the mission critical assets of the firm. They recently held a webinar with their partner eSentire to discuss these threats and how to abate them in order to create more certainty in this highly uncertain environment.
Whether for the facilitation of ecommerce, communication, or data transport and storage - from small consumer purchases to mission critical security and financial data for corporations – everything is online. And the reality is that while this access to information and commerce on a global level has opened up opportunities for so many, it has also created an environment full of risk as there are even greater means, motive and opportunity for cyber criminals to be successful in accessing and stealing data, and creating threats to the very foundations that support cyber activity.
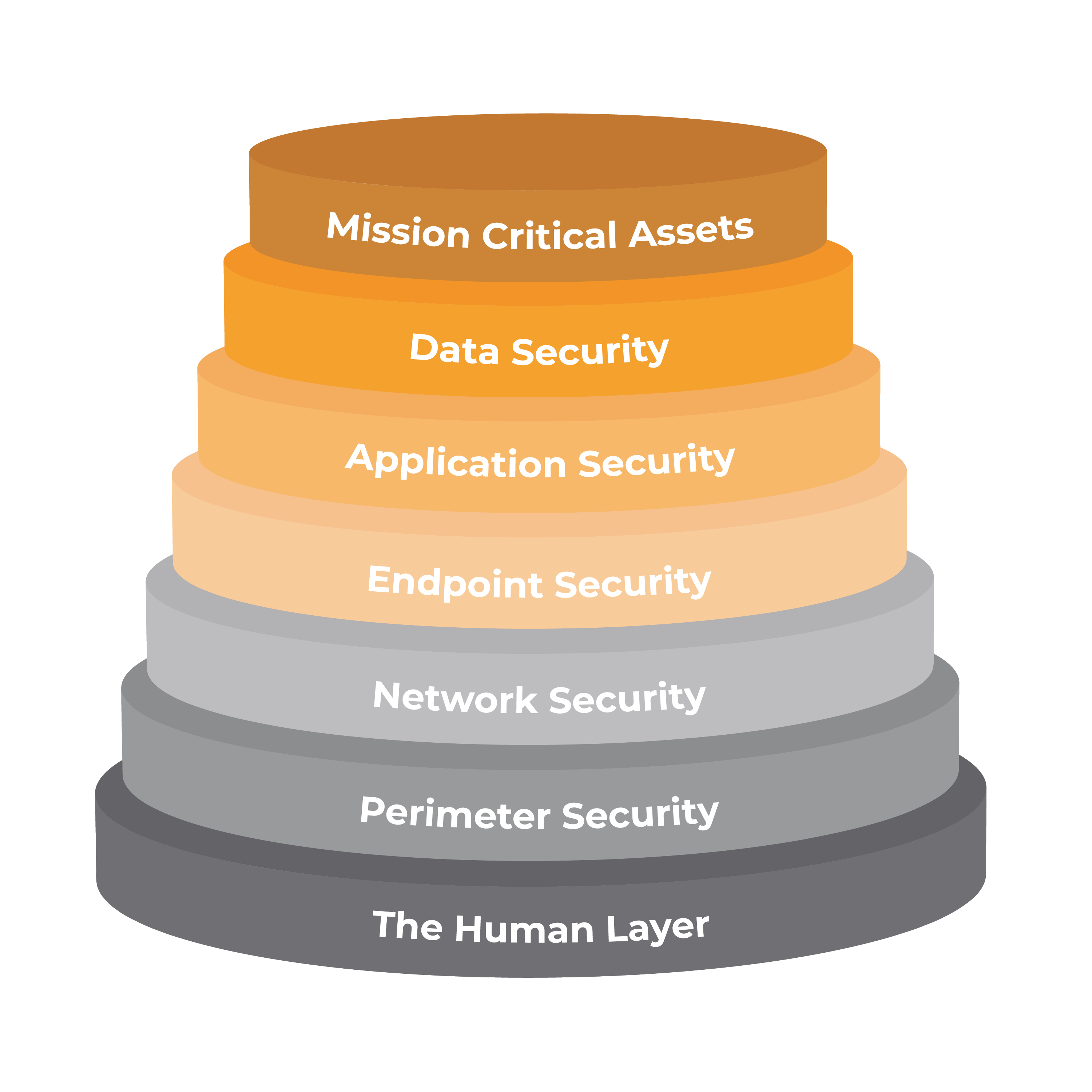
With global reach also comes mounting uncertainty. Corporations are concerned about protecting their customers, their data and even their very infrastructure. But because it is complex, many are not aware of all of the levels that are required to truly create and support an environment that ensures a highly secure environment. Apogee’s business model focuses on providing services that enable their clients to protect their clients’ assets through seven levels of security. The goal is to create defenses at multiple levels which in turn will enable their clients to develop certainty around how secure their environments are. It is important for firms to realize that hackers look for, and attack at all levels, thus all must be addressed with the ultimate goal of protecting the mission critical assets of the organization.
“The goal of having seven layers is to ensure that if one fails the others are in play to catch the incursion before it causes problems”
The seven levels identified by Apogee include:
- Mission Critical Assets – the part of the organization, product or service you are looking at securing
- Data Security – security controls in place to protect and monitor your data at rest and in transit
- Application Security – security controls and policies to protect access to your applications and how your applications access your data
- Endpoint Security – Controls to protect the connection between your computing devices and the network
- Network Security – Network controls and policies that protect your organizations network and prevent unauthorized access to your network and resources
- Perimeter Security – Physical and digital methodologies and policies that protect your overall organization
- The Human layer – Human security controls, policies and reporting that protect your critical assets from human threats
Apogee recently held a webinar with their partner, eSentire. This partner firm focuses on helping companies guard against threats to their application, endpoint, network and perimeter security. There are five factors that eSentire finds are a risk in any company’s ability to protect against threats: lack of visibility, limited response time, alert overload, security expertise gaps and outdated technology. These factors are highly impacted by the fact that individual corporations lack the headcount and expertise to respond to the multiple alerts and potential threats on a daily basis. Apogee and eSentire work with their clients to supplement their readiness through support and monitoring services.
Their services focus on the implementation of practices that reinforce security at multiple layers so that if one area is compromised, there is another layer to guard against unauthorized access and system disruption. In addition, they focus on providing support and expertise to effectively respond to alerts and potential threats faced on a regular basis, often a weak point for corporations. Apogee and eSentire monitor and build environments that protects their clients’ data assets. They have the expertise, processes and people in place to respond to and ward off threats that most corporations are not able to handle on their own.
Apogee has built its business around designing systems and processes that create CERTAINTY around the security of its client’s IT technologies. They focus on delivering security solutions that protect clients’ data, users, and connectivity as well as meet the compliance requirements of the business. They and their partners provide a level of expertise, tools, processes, and support that is dedicated to protecting against the rampage of attacks that threaten their business every minute of the day.
Apogee wants to bring that CERTAINTY to your business. So for a limited time, they are offering a free assessment of the 7 layers of security. They will review your current IT infrastructure, identify possible vulnerabilities, and provide you with the best course of action to create complete CERTAINTY around your business. Aim Higher and request an assessment so that Apogee can help you create a level of CERTAINTY that can help your business thrive.
















.png)
.png)